What Slows Mission Authorization and Deployment
Inherited CVE Backlogs
Vendor base images and open-source components introduce thousands of vulnerabilities before mission software even reaches development.
Gaps in Continuous Evidence
Security teams struggle to maintain consistent vulnerability and configuration evidence required for federal security reviews.
Security Baseline Drift
CIS, DISA STIG, and agency baselines often drift across development, staging, and production environments.
How RapidFort Reduces Mission Software Risk
Prioritize True Risk with Analyzer and Profiler Intelligence


Start Secure with Curated Near-Zero CVE Foundations
Continuously Reduce Exposure with Optimizer and CART

Outcomes Mission Programs Can Rely On
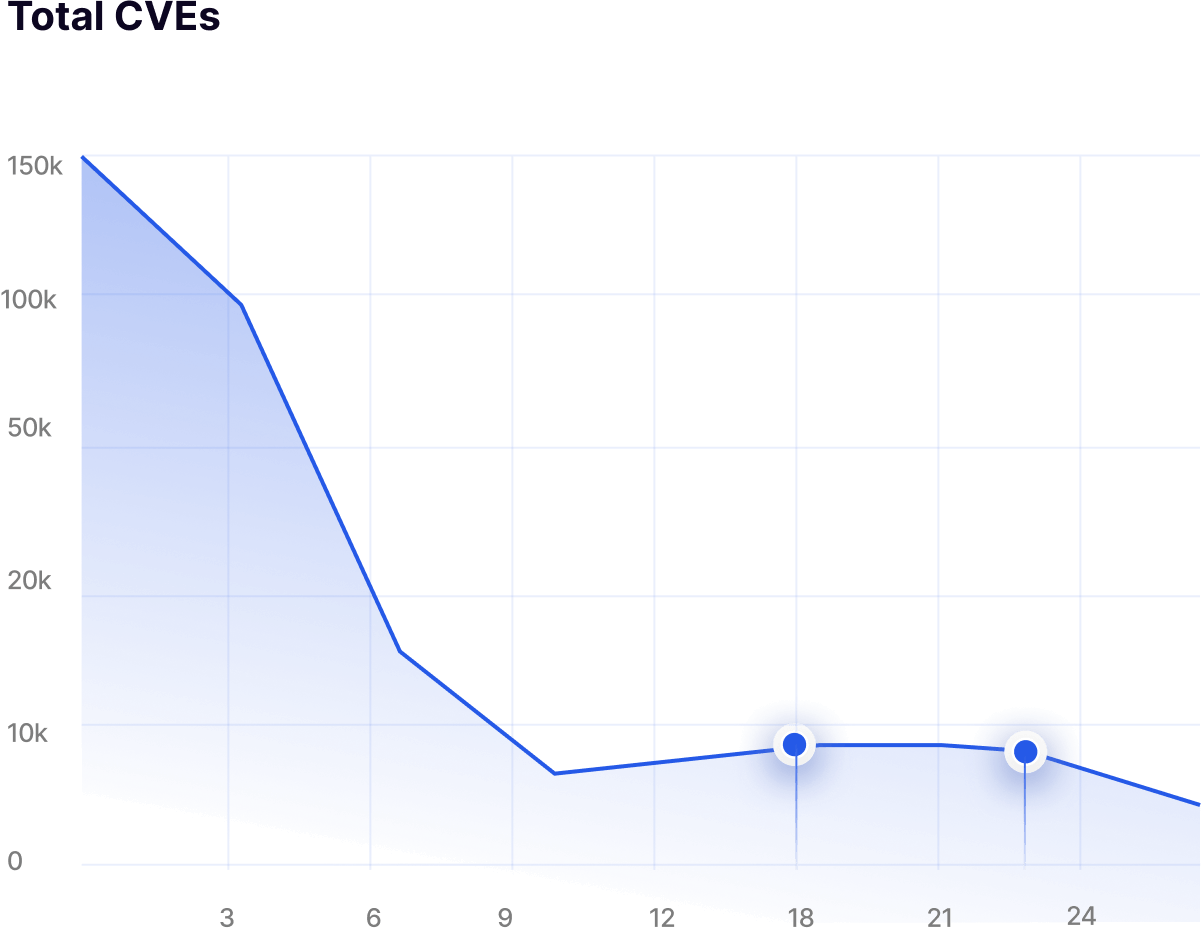
Up to 99.9% CVE reduction
Achieved through hardened base images and automated attack surface reduction.
Up to 90% attack surface reduction
Delivered by removing unused binaries and dormant runtime components.
Faster audit preparation
SBOM, RBOM, and configuration evidence remain continuously ready for review.
About 60% less manual remediation effort
Automation replaces repetitive vulnerability triage, exception handling, and patch cycles.
Regulatory Evidence Built Into Every Release
CMMC 2.0 and NIST 800-171
Continuous vulnerability visibility and hardened container foundations support secure software delivery for defense contractors.
FedRAMP and StateRAMP Readiness
Hardened container images and vulnerability visibility strengthen cloud security posture for federal environments.
NIST 800-53 and FISMA-Aligned Systems
Provide structured vulnerability evidence supporting federal risk management frameworks.
ATO and Zero Trust Initiatives
Reduce software attack surface and strengthen software supply chain security across mission systems.
Frequently Asked Questions
Answers to Your Most Common Questions


RapidFort helps organizations start secure and stay secure across the software supply chain lifecycle.
Teams begin with Curated Near-Zero CVE Images as a secure container foundation. RapidFort then analyzes container software, profiles runtime behavior, removes unused components, and validates security baselines to continuously reduce vulnerabilities and attack surface across development and production environments.


RapidFort Curated Images are production-grade container base images designed to start with near-zero vulnerabilities.
They are hardened using security benchmarks such as CIS and STIG, built on trusted Linux distributions including Ubuntu, Debian, Red Hat, and Alpine, and manually patched and rebuilt by RapidFort engineers to maintain a near-zero CVE state.
These images provide a secure foundation for building containerized applications.


RapidFort Community Images are free hardened container images available through RapidFort’s open-source community repositories.
They are optimized using RapidFort’s Software Attack Surface Management approach, which removes unused packages and dependencies to significantly reduce vulnerabilities caused by unused software.




